Back in a Spell – Speaking of…

Google Uncovers 'Initial Access Broker' Working with Conti R
iGEMPulse/Old/Scrapy/igem/abstracts.json at master · ilia-kats
Bitter APT Hackers Add Bangladesh to Their List of Targets i
cookbook-2nd-data/troll.csv at master · ipython-books/cookbook-2nd

Back in a Spell (The Witches of Thistle Grove, #3) by Lana Harper

Back in a Spell — Raccoon River Press
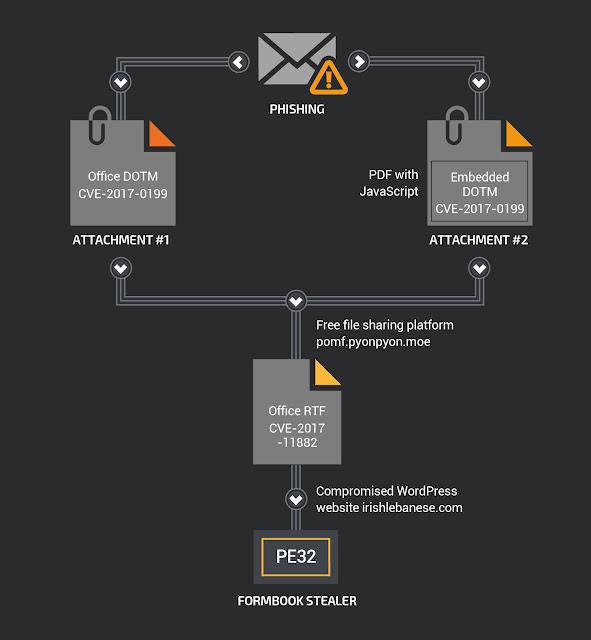
My Little FormBook - vulnerability database

goodnews/training/requests.txt at master · s-j/goodnews · GitHub

Back in a Spell (The Witches of Thistle Grove, #3) by Lana Harper
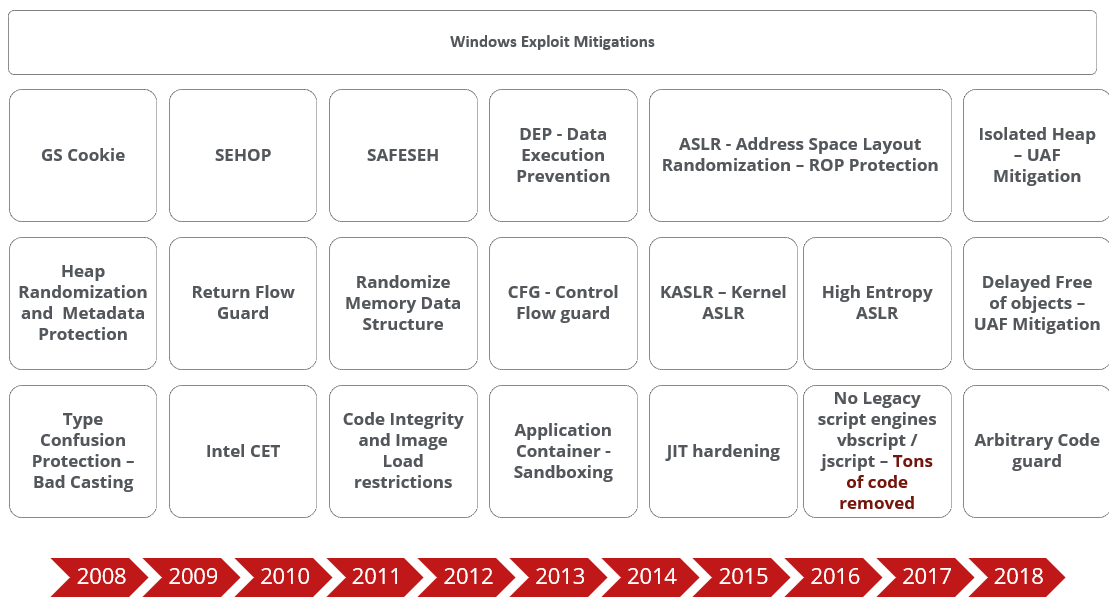
Beyond Memory Corruption Vulnerabilities – A Security Extinc

IT threat evolution Q3 2022 - vulnerability database

New Exploit Lets Malware Attackers Bypass Patch for Critical
Insults/Insults/Data/Inputs/test.csv at master · cbrew/Insults

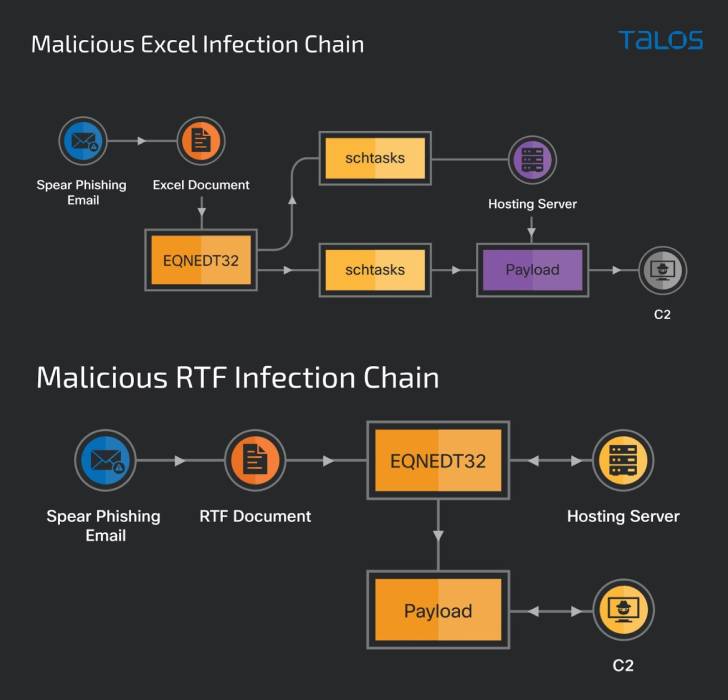
LodaRAT Windows Malware Now Also Targets Android Devices
Back in a Spell – Speaking of…
- Best Price $ 5.50. Good quality and value when compared to tickets.dezwitsalhal.nl similar items.
- Seller - 354+ items sold. Top-Rated Plus! Top-Rated Seller, 30-day return policy, ships in 1 business day with tracking.
People Also Loved
-

Louis Vuitton Green Crossbody Bags
Buy It Now 27d 18h -

Authentic Louis Vuitton Stylish Rings LV 18K-Gold Filled DIY
Buy It Now 21d 21h -

Louis Vuitton Silver Tone Gamble Crystal Bracelet Louis Vuitton
Buy It Now 9d 13h -

Louis Vuitton Speedy 35 Bandoulière, Canvas, Damier Ebene - Laulay
Buy It Now 4d 14h -

Louis VUITTON×NIGO 20Aw Printed Crew Neck Sweatshirt HJY13W UYR/VCCM09
Buy It Now 19d 17h -

PurseForum Community — ThemeHouse Portfolio
Buy It Now 9d 14h -

Louis Vuitton Monogram Petite Malle Souple Black
Buy It Now 24d 18h -

Louis Vuitton Monogram Cigarette Case Mobile Etui Phone Holder 553lvs611
Buy It Now 26d 8h -
Jules Style Diary: Louis Vuitton Monogram vs. Damiere Ebene
Buy It Now 10d 10h -

Pin on Clothing inspiration
Buy It Now 22d 14h -

A Royal Louis XV Literary Tapestry, from the Story of Don
Buy It Now 15d 11h -

Fakta Unik Tas Louis Vuitton yang Dibanderol Puluhan Juta Rupiah, Tahan Air dan Api? - Semua Halaman - Stylo
Buy It Now 3d 14h -
Louis Vuitton Monogram Cream and Brown Silk Scarf
Buy It Now 21d 7h -

Jual Sepatu Louis Vuitton Wanita Original Terbaru - Oct 2023
Buy It Now 12d 7h -

Louis Vuitton, Bags
Buy It Now 2d 18h -

Louis Vuitton 2008 Pre-owned Camouflage Monogram Carry 60 Travel Bag - Green
Buy It Now 27d 16h -

Prada Lux Tote Handbag 375814, Extension-fmedShops
Buy It Now 8d 23h -

Saint Laurent Y Cabas Bag in Blue
Buy It Now 13d 16h -

We Bare Bears Tote Bag for Sale by plushism
Buy It Now 20d 12h -

1-155/ LV-NF-PM3) Bag Organizer for LV Neverfull PM - SAMORGA® Perfect Bag Organizer
Buy It Now 2d 14h -

El bolso de Louis Vuitton de 3.200 euros que imita una bolsa isotérmica para congelados
Buy It Now 6d 12h -

Diy Pop Bag Charm · A Pegboard Bead Charm · Pegboard and Jewelry Making on Cut Out + Keep
Buy It Now 11d 19h -

Chewy Designer Dog Backpack Harness | Supreme Dog Garage
Buy It Now 23d 11h -

Nike Air Force 1 '07 LV8 - White
Buy It Now 21d 20h
